Security Assessment (SA)
Our team of experienced security professionals will examine your systems to identify security postures of your current IT Infrastructure and address vulnerabilities that could be exploited by malicious actors.

3E SA Services:

Web Application Assessment
This assessment identifies security risks in your web applications e.g. WordPress. Experts evaluate vulnerabilities such as SQL injection and XSS to prevent information leaks or unauthorized access. Based on the findings, we propose actionable improvements to enhance the safety and reliability.
Platform Assessment
Our platform assessment ensures your operating system, middleware, and database are free from vulnerabilities. We check an organization’s networks and systems or Wi-fi for improper configurations, known risks, and unnecessary services, providing strategies to minimize both external threats and internal risks.
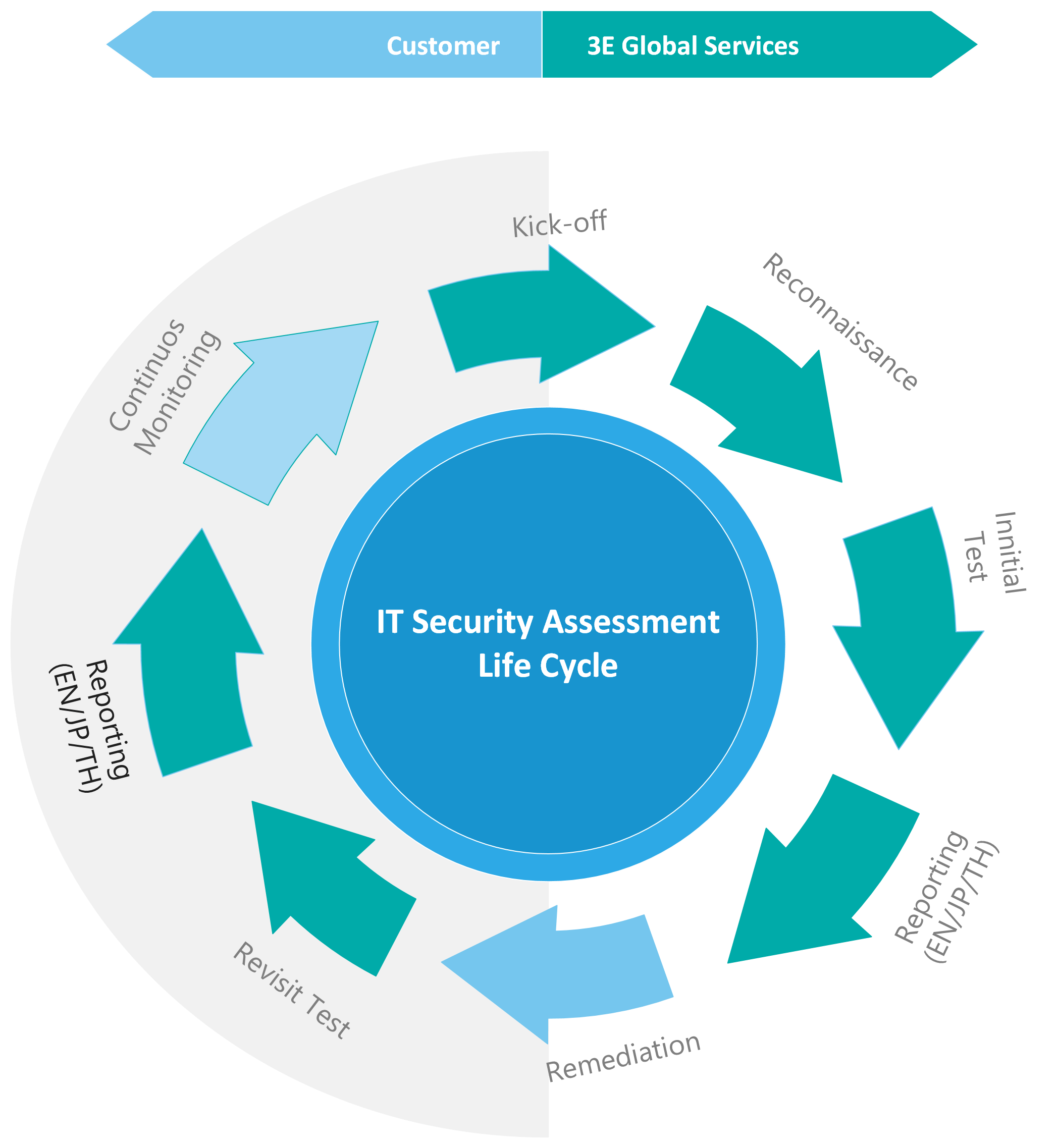
SA Lifecycle
Stages for Security Assessment Service
Detail Description
Kickoff: Meeting to gather requirement and summarize the scope
Reconnaissance: Survey of the target environment for designing a security assessment best practice
Test: Performance a Web Application Assessment or Platform Assessment
Reporting: Comprehensive reporting of findings and proposed countermeasures
We follow the Leading-Industry Testing Standard
Top 10 : Web Application 2022
OWASP Application Security Verification Standard 4.0

TOP 25 Most Dangerous Software Errors (CWE)
CVE, CVSS standards
FAQ
What is a vulnerability assessment?
It is a process to identify security weaknesses in web applications, systems, and platforms. Recommendations for risk mitigation are provided based on the findings.
What areas are assessed?
・Web Application Assessment: Forms, authentication, session management, APIs
・WordPress Assessment: Plugin/theme vulnerabilities, misconfigurations
・Platform Assessment: OS, middleware, database settings, and activity
Can the assessment be conducted remotely?
Yes, remote assessments are standard. On-site assessments are available upon request and specific requirements.
How long does the assessment take?
Depending on the scope and scale, the process typically takes 1-2 weeks. The exact timeline is shared during the quotation phase.
How are results reported?
A detailed report is provided, highlighting vulnerabilities, risk evaluations, and recommended countermeasures. Follow-up meetings or consultations can also be arranged.
What should be prepared for the assessment?
・Remote Access Permissions (for scanning)
・System details, including application URLs, global IP, or FQDN
Will the assessment impact system performance?
Non-disruptive methods are used to minimize impact. Any required load testing is pre-arranged.
What does the WordPress assessment include?
Vulnerability checks for plugins, core files, themes, access rights, and file structures.
What are the benefits of a vulnerability assessment?
It enables proactive risk management, helping avoid data breaches and service disruptions.
Is re-assessment available?
Yes, post-remediation assessments are available to confirm the resolution of vulnerabilities.

3E Global (Thailand) Co., Ltd.
2 Jasmine Bldg., 22nd Fl., Soi Prasarnmitr(Sukhumvit23), Sukhumvit Rd., North Klongtoey, Wattana, Bangkok 10110, Thailand

